Remember those times when using the Internet and (owning a personal computer) was a luxury? Those times were much safer, weren’t they? The more we become dependent on the Web, the more we expose ourselves to various security- and privacy-related risks.
Besides your circle of friends and people you want to get in touch with, the Internet is full of scammers and spammers, malvertisers and malware droppers, and dubious “third party” services impatiently looking forward to collecting your personally identifiable information. The more the Internet evolves, the more dangerous it becomes.
If a user is smart enough and knows a thing or two about cyber security, they might be able to escape some of the dangers the big online village hides. The very first thing to keep in mind, however, is that dangers lurk not only in the “darkest” places (like visibly illegal websites). Thanks to the evolution of malicious tactics, even completely legitimate websites and services can be compromised. And they are, more often than not!
Unfortunately, we’ve been observing an uptake in malicious attacks on social media, financial and healthcare institutions, file sharing and torrent sites, and popular entertainment websites. Attack vectors change, and their scope is broadening with every single day. With that said, you should definitely know your average online risks, as you won’t see a “Danger Zone!” sign identifying them for you. (You might notice other signs that help identify malicious behavior, though.)
Now is the perfect moment to outline the riskiest places on the Web these days. Even though knowing the traps is not too likely to stop you from visiting the about-to-be-mentioned online spots, it’s good to use the latter with caution. Plus, knowing will make you want to improve your online security, wouldn’t it?
Social Networks and Informational Portals
You love social networks because they connect you with people you care about but are far away, on one hand. On the other, social networks definitely help bring your social life to life. Where else will you learn about nearby events you are interested in if not on Facebook?
However, the extensive use of social media channels hides its risks, most of which directly endanger the data you have uploaded there, as well as your login credentials and personal details.
Let’s take data breaches, which have already compromised LinkedIn, MySpace, and Tumblr, among others. Data incidents are no joke since they put your login credentials and your account at risk of further exploits. Just imagine all the wonderful outcomes of your Facebook getting hacked!
Your login credentials (email and password) can be used against you. Hackers can easily match your profile with your other social accounts.
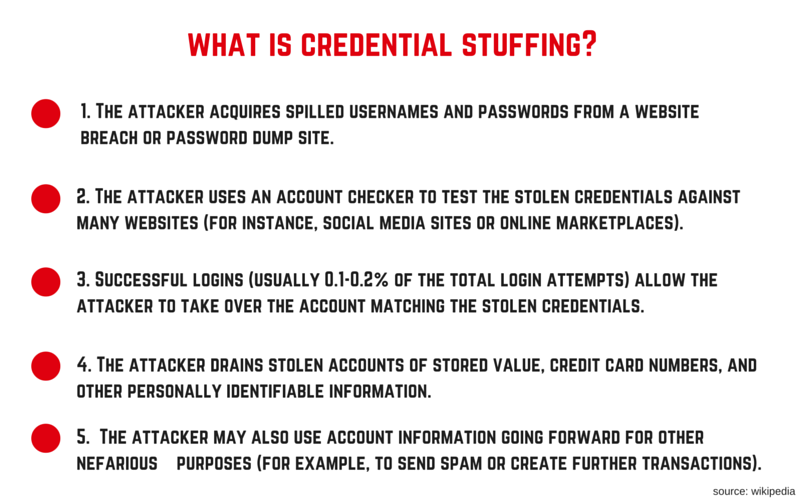
Have you heard of credential stuffing?
Credential stuffing is the automated injection of breached username/password pairs in order to fraudulently gain access to user accounts. This is a subset of the brute force attack category: large numbers of spilled credentials are automatically entered into websites until they are potentially matched to an existing account, which the attacker can then hijack for their own purposes.
If your account has been through a malicious takeover, it can be used to spread malware across your friends list. Or it can be used for other purposes, depending on your job position or overall social status (the more popular you are, the further the damages can go). We are yet to learn all the fallouts of data breaches, brute forcing, credentials stuffing, and any other big data issue really.
Related: The Big Data Obsession
Facebook and social media in general are often leveraged in suspicious campaigns which usually end with a piece of malware or spyware being dropped on targeted systems. Our interconnection via the Internet and other rising technologies enables cyber criminals to carry out various attacks, like phishing and waterhole attacks. In many cases, cyber criminals want to obtain access to the largest possible pool of victims. Ever growing social media sites like Facebook, Twitter and LinkedIn give malicious minds an easy way in. According to many researchers, waterhole attacks stemming from social media will continue to grow.
Furthermore, TrendMicro research on waterhole attacks indicates that:
Attackers have used websites frequented by one or more members of a target group to infect these individuals and their devices with malware. For example, if a black hat is looking to go after a particular business and notices through observing network activities that a number of employees often use an informational website related to that industry, the hacker could place malware on the site – or create a legitimate-looking fake page – to lure staff members into infecting the network.
In early February 2015, a specific raid on the social media involved a pornography-based Trojan horse targeting users of Facebook. It’s definitely not the first or last venomous endeavour aimed at users of the popular social media (and deploying adult content to do so).
Compromised CMS (WordPress, Drupal) Websites
As we have already written, outdated CMS websites are at huge risk of hacking and malware infections. Mossack Fonseca, the law firm associated with the Panama Papers breach, already became a victim in such a scenario. Other big companies are also prone to hacking, as revealed by a research conducted by US security vendor RiskIQ.
CMS vulnerabilities are a common denominator of many of the successful attacks we read about. With the ubiquitous nature of CMSs in driving the web experience, potential risks lurk for virtually all organizations. According to W3 Techs’ Web Technology Surveys, 65 percent of all websites using a CMS use WordPress or Drupal, which use open-source code that’s available to all — including malicious actors looking for exposures to exploit.
Vulnerable CMS websites bring risks not only to enterprises but to average users as well. Using compromised websites is an attack vector favored by many cyber criminal groups. For example, in a recent ransomware attack bad JavaScript code was added to the source code of hacked WordPress and Joomla websites. The attack was done in a manner that disguises the malicious code and made it look like a social plugin.
Other high level security risks endangering websites are malvertising attacks and automated attacks via exploit kits. To avoid becoming a victim in any malicious scenario, keep your software up-to-date (malware operators just love to exploit vulnerabilities) and your system protected by anti-malware and anti-ransomware tools.
Online Gaming Websites and Platforms
If you’re a keen online video gamer, continue reading carefully.
The gaming industry is definitely among the most profitable ones, pulling in multibillion-dollar revenue. Did you know that in 2014 PC and MMO (massive multiplayer online games) generated revenue of $24 billion? Online gaming itself made $21 billion. It’s only natural that hackers and spammers would drool over the cake, and would like a large piece of it.
There are plenty of online gaming websites ridden with malware:
- anywhere-games(.)com
- galacticflashgames(.)com
- gamefactoryinteractive(.)com
- games-digest(.)com
- mariogamesplay(.)com
- towerofdefense(.)com
- PlayLunar(.)com
Let’s take the PlayLunar website. PlayLunar(.)com can easily affect your PC with the aid of third-party install setups. You might install an adware program related to PlayLunar on your machine without even realizing it. Thanks to packages and freeware installers, this happens quite a lot. Unwanted, sometimes silent downloads of PUPs are a major online security problem.
ESG researchers suggest that computer users who wish to play online games leave their anti-virus or anti-spyware protection running at all times especially when attempting to play an online game. The malware-laced sites uncovered recently are only small percentage of other potentially infected gaming sites on the Internet.
Porn Websites
Just last year, some of the most popular websites like Pornhub and YouPorn were hit by an attack that “forwarded” malware to their visitors.
A third-party advertising provider was giving visitors suspect pieces of code that then gave users malware. Since the code was sneaked in through an advertising network, the two sites didn’t actually have any role in providing it themselves, though it could have hit anyone visiting the site.
That being said, it’s only logical Pornhub recently joined the bug bounty initiative and launched a program on HackerOne’s platform, which aims to protect and enhance the site for their 60 million daily visitors.
File Sharing and Torrent Websites
Downloading copyrighted movies and television shows is often followed by malware infestations. According to a report by RiskIQ for 2015, users are 28 times more likely to infect their machines with malware from torrent sites than they are from visiting legitimate and licensed content providers. Actually, one-third of websites with “stolen” content had malware and 45 percent required only one visit to trigger the download of malware.
Furthermore, one-third of the websites had links to malware and were employed for fake downloads, drive-by downloads and malvertising, malicious pop-ups and bogus download links. Worse, this number didn’t take into account malware infections triggered by clicking on malicious ads or from downloading shared files on torrent websites. Overall, visiting a torrent website was calculated 28 times more dangerous than visiting a legitimate streaming/download provider.
Related: Downloading Fake Torrents
Another research paper titled “Digital Bait” indicates that one of every three torrent websites is loaded with malware and PUPs attacking popular browsers. The result is approximately 12 million users exposed to malicious software each month.
If you’re a user of file sharing and torrent websites, we highly advise you to install a strong anti-malware program. You should also consider disabling Adobe Flash Player and Java. Attackers often leverage them.
Chrome Web Store
About a year ago, Google started a quest to chase bad extensions away from Google Web Store. According to a Google-funded study presented at the IEEE Symposium on Security and Privacy tens of millions of Chrome users had some kind of add-on malware installed on their systems, which is 5% of total Google traffic. Almost 200 plugins were scrubbed from Chrome App Store. The whole research brought attention to the overall state of security of Google’s market place.
Related: Google Knows about You, Know about Google
Even though Google is doing their best to keep the Store malware-free, when something sneaks in, it’s usually quite bad.
Here are several examples of bad extensions jeopardizing users’ security and privacy:
- AddToFeedly (laced with the SuperFish adware)
- WebPageScreenshot (transmitting user information to a single IP address in the United States)
- Adicionar Ao Google Chrome (which hijacked Google accounts)
Despite Google’s efforts, Malwarebytes researchers detected yet another dangerous extension in January 2016. This is what they wrote:
We recently came across a malvertising incident pushing a site forcing us to install a Chrome extension called iCalc. There was no clean way of closing the window and refusing to install this program. As soon as the user moved the mouse close to the address bar or near the close button, an annoying dialog accompanied by a stern audio message would pop up.
At least 1,000 users downloaded the extension before it was removed by Google. The moral of the story? Google cannot always stop malware, so you should be the one taking care of your own security. Always research the extensions you plan to install, and treat them like all the suspicious apps in Android’s Google Play.
Spam Emails in Your Inbox
Spam emails are a huge culprit for present malware and ransomware infections. For instance, Locky and Cerber crypto viruses are yet again being spread in aggressive spam campaigns. Ransomware is often distributed in malicious Word documents. Users are usually tricked into enabling malicious macros.
In most cases, macro malware resides in Microsoft Word or Microsoft Excel documents. Many malware infections have started this way. The malicious documents are usually spread via spam email attachments, or inside ZIP files attached to the spam email.
Indeed, aggressive spam campaigns are the current distribution method, once again employed by Locky. The malware operators are spreading cleverly crafted spam messages that appear to be sent from trustworthy sources in accordance with the targeted country. The infection process requires the user enabling the Macros within the Word document. This is when the actual infection takes place.
To escape becoming a victim of spam and respectively malware, you should disable macros in MS documents, you shouldn’t open suspicious emails, and you should think of anti-spam measures. Use anti-spam software, spam filters, aimed at examining incoming email. Such software isolates spam from regular emails. Spam filters are designed to identify and detect spam, and prevent it from reaching your inbox. Make sure to add a spam filter to your email. Gmail users can refer to Google’s support page.